Encrypting disks in linux environments
- A comprehensive guide containing automatic decryption at boot and live extension.
- Posted by Kostas KoutsogiannopoulosAug. 26, 2024
Absolute privacy for sysadmins
- Is privacy a feasible goal? 5 simple rules that can keep your data protected.
- Posted by Kostas KoutsogiannopoulosFeb. 20, 2021
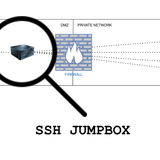
SSH bastion/jump host
- Use -with total transparency- a jumpbox to access your private network.
- Posted by Kostas KoutsogiannopoulosOct. 24, 2020
Content Security Policy header
- Monitor, control and report disputed resource loading on your web pages.
- Posted by Kostas KoutsogiannopoulosMarch 29, 2019
HTTP Referrer Policy header
- How to control your http references on your web pages like a pro.
- Posted by Kostas KoutsogiannopoulosFeb. 8, 2019
Distributing fail2ban actions
- Using fail2ban and redis under ansible's orchestration for common good.
- Posted by Kostas KoutsogiannopoulosDec. 29, 2017
SSH server as SOCKS proxy
- Securing internet access from public places using your SSH server.
- Posted by Kostas KoutsogiannopoulosJune 26, 2016
Fail2ban for dovecot and postfix
- Fail2ban configuration example for dovecot(POP/IMAP) and postfix(SMTP).
- Posted by Michael CossenasMarch 23, 2016